Your own personalised stalker
It always seemed slightly creepy that your computer shows advertising that is strangely accurately targeted at things you might have been interested in. On the surface, that seems quite useful. If you have to tolerate ads on your screen, at least having them show things you were interested in seems helpful.
Instead, we wonder how the system knows. It feels like a breach of our privacy.
It all starts when you install an app, and it pops up a question asking for permission to use your location, and/or your camera and/or your microphone.
This is useful for advertisers. For example, they can use your location. If the app reports this back to the content provider, they can match up your location and compare you to other people nearby. If you tend to go to the same places as other people, you are probably interested in the same things, so an advertiser might use that assumption to present advertising to you, or other people that you spend time with.
That does sound a bit overreaching, but we reluctantly agree to the presented terms simply because we want to use the app. If that is a condition of use, and we want to use the app, then we agree.
So, now we are seeing consumers getting the choice to push back.
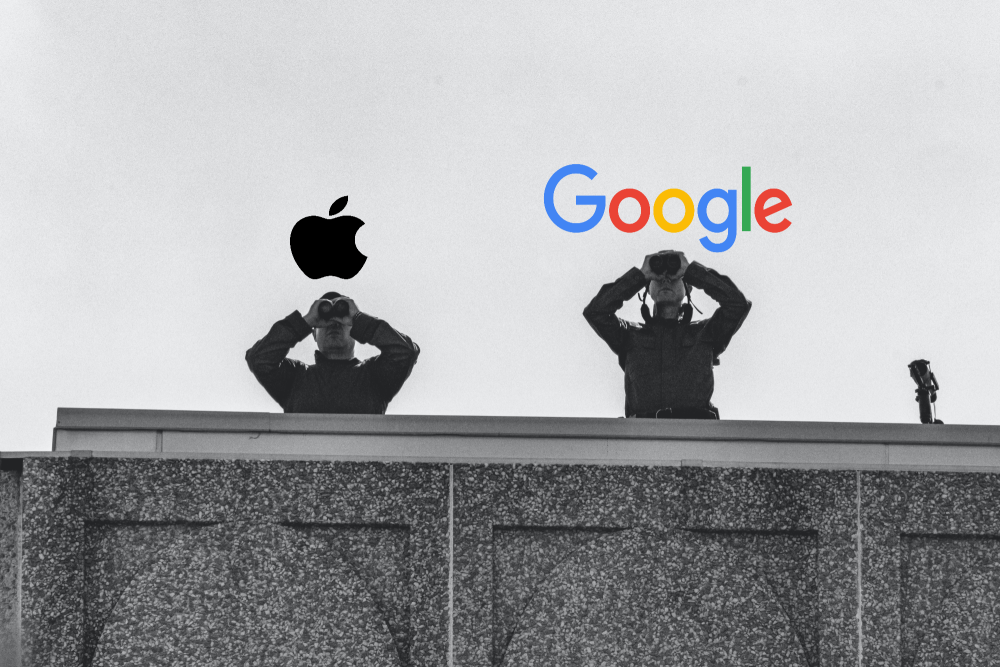
Apple
Now, with iOS15, Apple are saying that you will get to see what apps are accessing your data. You will be able to see when an app used that permission, and there it was sent to. Whether that list of third party sites is any use or not is meaningful is unclear.
Not quite as advanced but following quickly behind is Google Android. With Android 12, you will have the option to de-personalise your data. They will still track usage, but won’t link it back to you.
Is there any truth to the rumour that your phone or TV is listening to you, and presented content based on private conversations it overhears?
Given how poor the voice recognition is on phones , cars, or tools like Alexa or Siri, its pretty evident this can’t be reality. If it, is, then heaven only knows what it thinks it’s hearing. The voice recognition tools are getting better all the time, but there is a long way to go.
Christmas is coming. But will you get a visit from Santa or from a grinchy hacker?
Protecting Yourself from Cyber Threats While on Holiday We're more vulnerable than normal to hackers at this time of year. Unfortunately, the hackers know it and tend to be more aggressive.In the rush up to Christmas, there's normally so much to do that we're all that...
Understanding Your Microsoft Secure Score: Why Your Percentage May Drop (While Your Security Improves)
Important Update for KARE Foundation Subscribers If you've noticed your Microsoft Secure Score percentage decreasing recently, don't be alarmed. Your security hasn't weakened. In fact, Microsoft is making significant enhancements that will ultimately make your...
Stop Searching Stock Photos: Microsoft Copilot Now Creates Custom Images Inside Your Documents
Microsoft has quietly added a capability to Copilot that eliminates one of the most frustrating parts of document creation: finding the right image. Instead of searching through stock photo libraries or hiring designers, you can now generate custom images directly...
AI Just Got Scary Good (and Scary Affordable): 5 November Breakthroughs
November 2025 marked the moment AI stopped being a curiosity and became a genuine business advantage. Don't wait for your competitors to get the jump with these new capabilities. Here are the five developments that changed the game—and what they mean for your...
Why Waiting to Replace Your PCs Could Cost You Thousands
If you still have Windows 10 PCs to replace, what does this mean for you?Kinetics is at the Canalys industry conference in Vietnam this week, and we've just been warned about a trend that's going to impact all of us in the next few months. It's even worse if you are...
Cybersecurity Alert: Holiday Phishing on the Rise — And Attackers Are Using Your Own Tools
As the festive season kicks into gear, so too does the cybercriminal playbook. We’ve noticed a spike in phishing attempts disguised as “pre-Christmas party invites”. While the festive spirit is infectious, so too is the threat. These aren’t just generic holiday...
Document Automation Macros for Word
Recently a client asked for help to create an automated document creation system.Problem: The client had hundreds of similar documents that needed to be created quickly, consistently and accurately Answer: Microsoft 365! Attached is a brief video that runs through how...
Webinar Replay: Reclaim Your Time: How Smart Microsoft 365 Use Saves 10+ Hours Per Week
Transform Daily Tasks with Microsoft 365 Tools You Already Own Stop reinventing the wheel every time you write a proposal, create a report, or process a form. Most New Zealand businesses use Microsoft 365 for email, document storage, and video calls, but they miss the...
Looking Back at 2020: The Year That Transformed Business IT Forever
Looking Back at 2020: The Year That Transformed Business IT Forever As we step into 2025, it's worth reflecting on a year that permanently altered the trajectory of business technology. Five years ago, 2020 didn't just bring new software releases and hardware...
2025 Q4: Cyber Landscape Update (are you still feeling lucky? New Zealand’s Cyber-threat landscape demands action)
Why This Brief Matters A cybercriminal only has to be lucky once. You have to be lucky every minute of every day. That remains the stark reality for kiwi businesses in Q4 2025. This isn't another dry technical report filled with acronyms and alerts. Kinetics has...